WEP
(税込) 送料込み
商品の説明
■WEPタイプのフライトジャケット。上品な風合いの生地を使用することでミリタリー感を抑え、様々なスタイルに合わせることができる一着に仕上げられています。左胸のマジックテープはオス側を取り外すとブランドロゴが現れるデザインとなっています。右袖先にもマジックテープを配置。裏地にはオリジナルのチェック生地を使用しています。※オリジナルハンガー、カバーが付属します。
- 原産国
- 日本
- 素材
- 表地:ポリエステル65% レーヨン35% 裏地1:ポリエステル100% 裏地2:ポリエステル100% リブ:アクリル60% ウール40%
- 特徴
- 無地
- ジップアップ
- 関連カテゴリー
- ジャケット/アウター
- ミリタリージャケット
- 性別タイプ
- メンズ

Wired Equivalent Privacy - Wikipedia

WEP Crack Method in Wireless Networks - GeeksforGeeks

Security + 1.2 Wireless Attacks WEP & IV
Wired Equivalent Privacy (WEP) - CyberHoot

Schematics of the WEP protocol used to control access to the WLAN

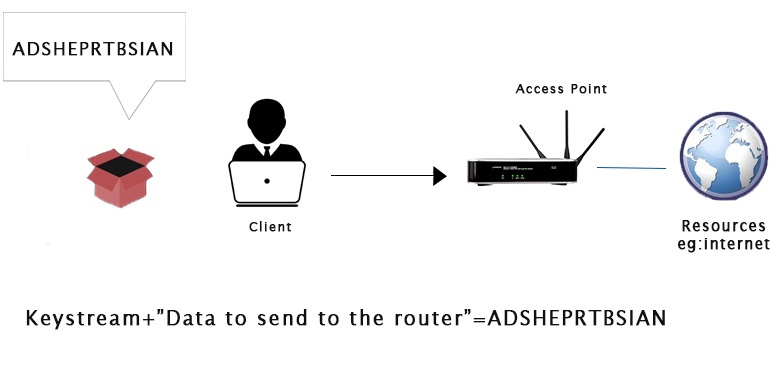
IV Attack in WEP - The Security Buddy
WPA vs WPA2: Which WiFi Security Should You Use?

Illustration of a Wired Equivalent Privacy (WEP) weakness. The
What is Wired Equivalent Privacy (WEP)?

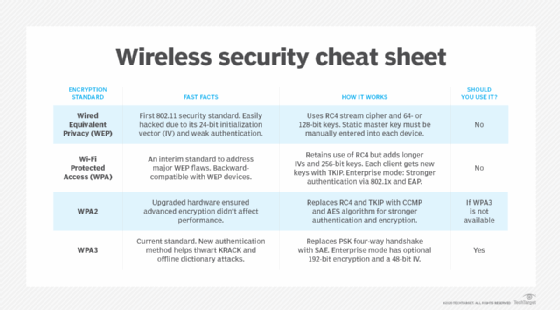
WEP, WPA, WPA2, and WPA3: Differences and Comparison | Gridinsoft
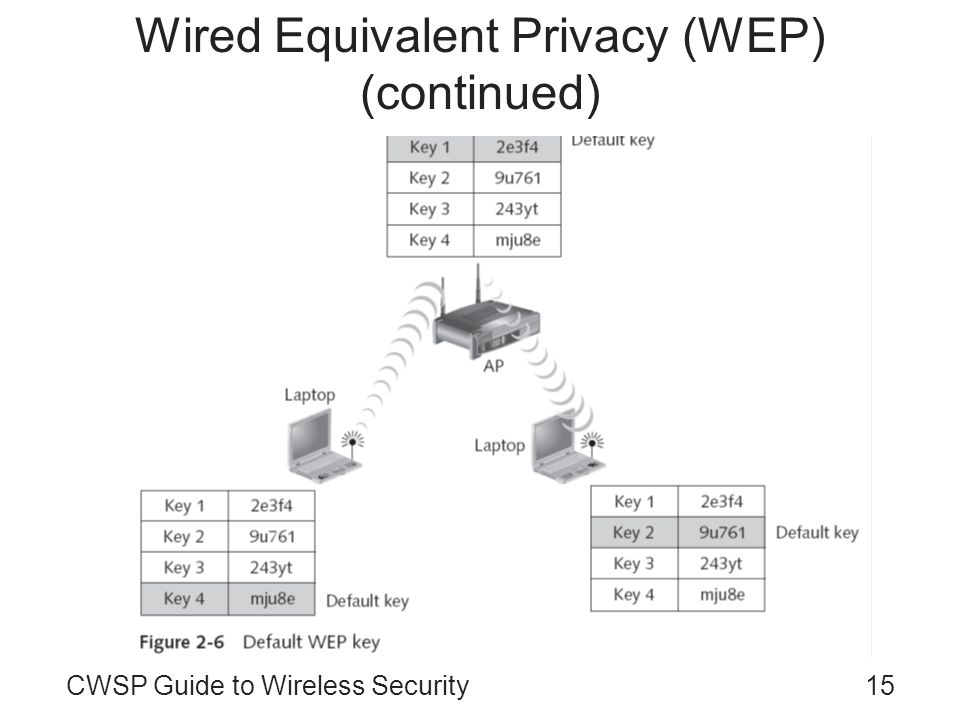
Wired Equivalent Privacy (WEP)
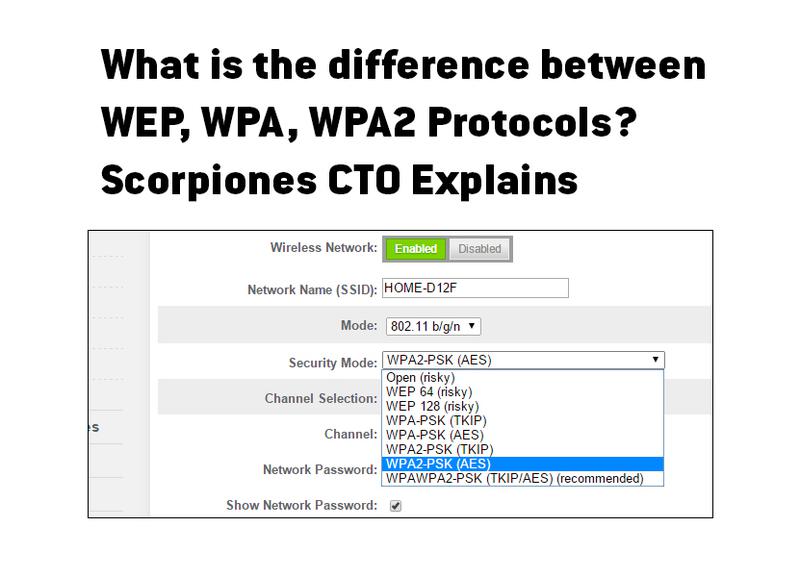
Scorpiones Group | The Difference Between WEP, WPA, and WPA2 Wi-Fi
Schematics of the Wired Equivalent Privacy (WEP) protocol used to

WEP Australia | Melbourne VIC
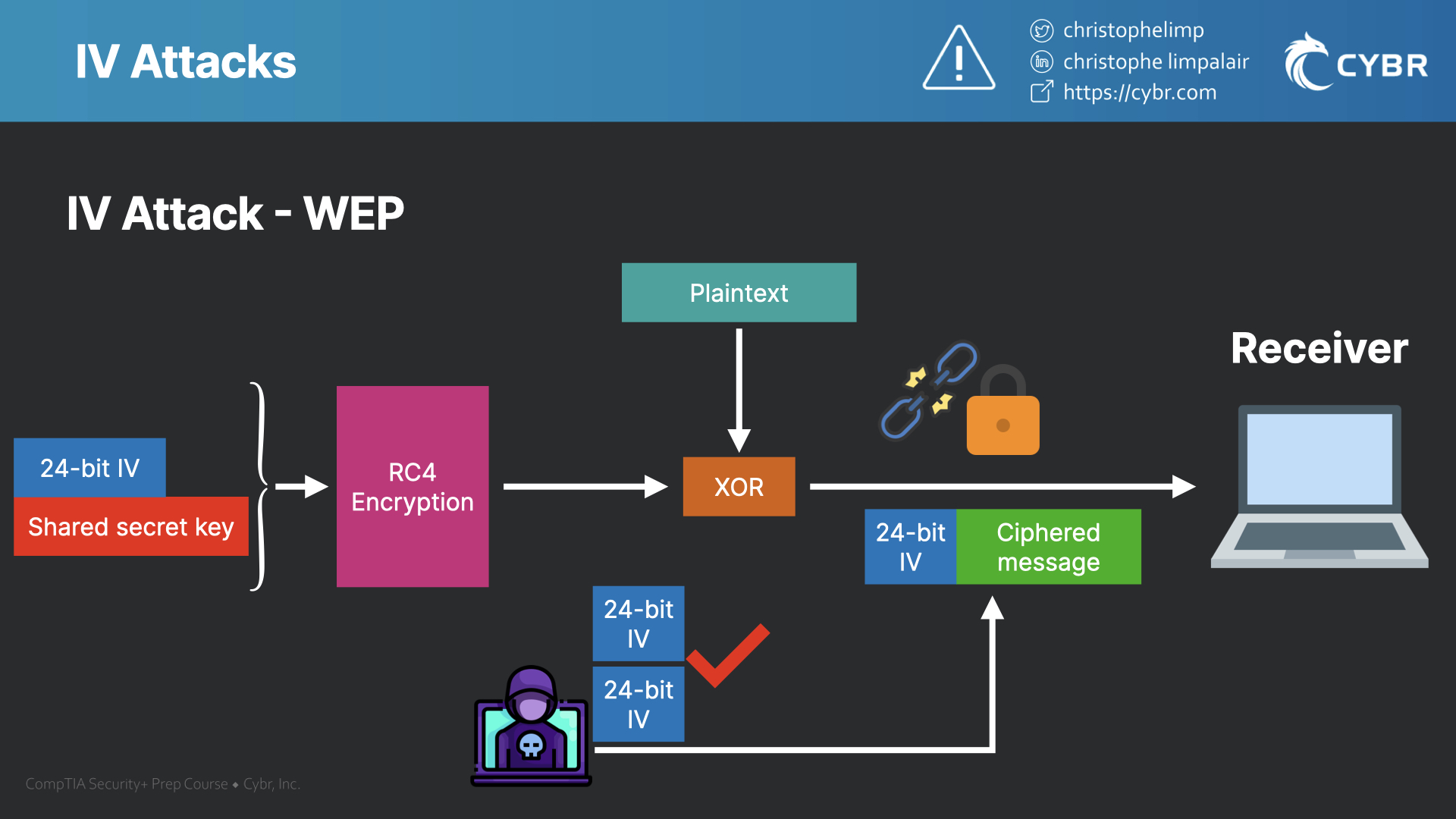
Initialization Vector (IV) attacks with WEP - SY0-601 CompTIA

Why WEP Should Not Be Used in Wireless Networks Today
WEP Introduction - javatpoint
Illustration of a Wired Equivalent Privacy (WEP) weakness. The
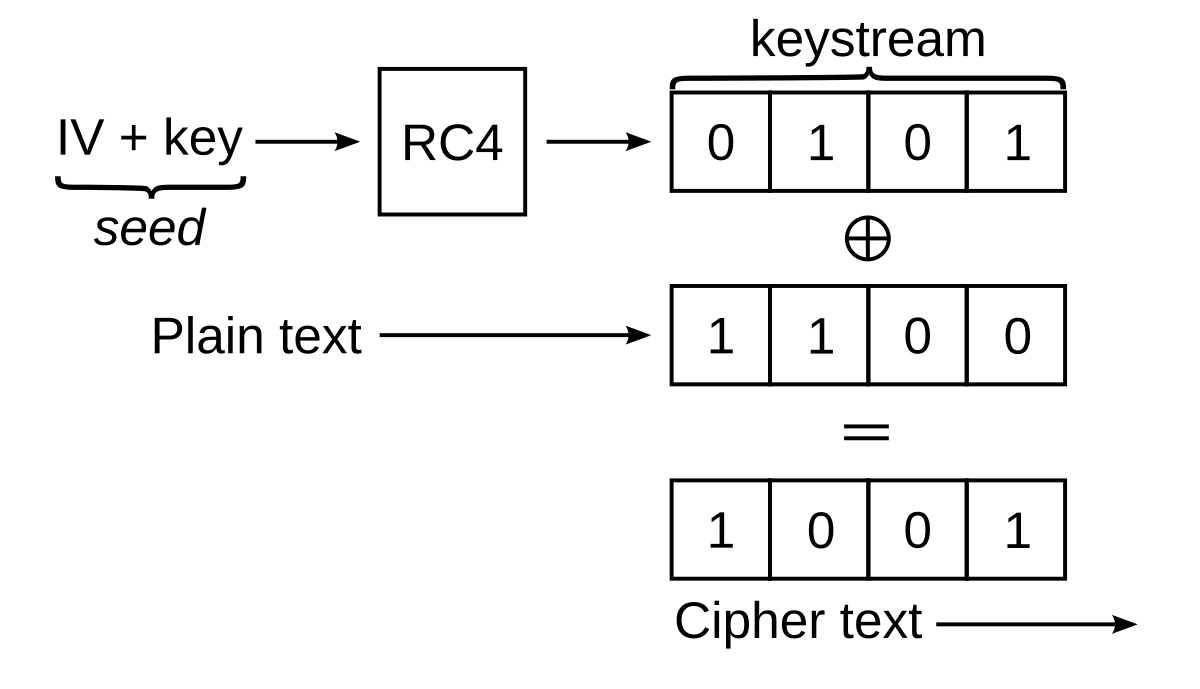
File:Wep-crypt-alt.svg - Wikipedia

Enhancing RC4 algorithm for WLAN WEP protocol | Semantic Scholar

WEP vs. WPA vs. WPA2 vs. WPA3 | FS Community
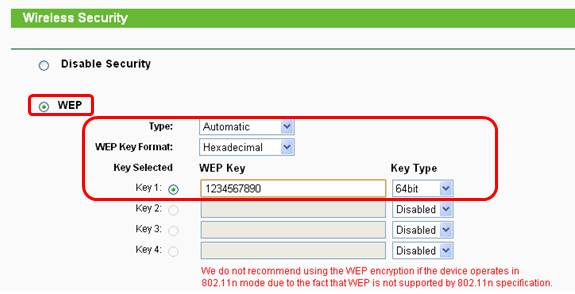
How do I secure/protect my wireless network by using WEP
What is WEP - Javatpoint

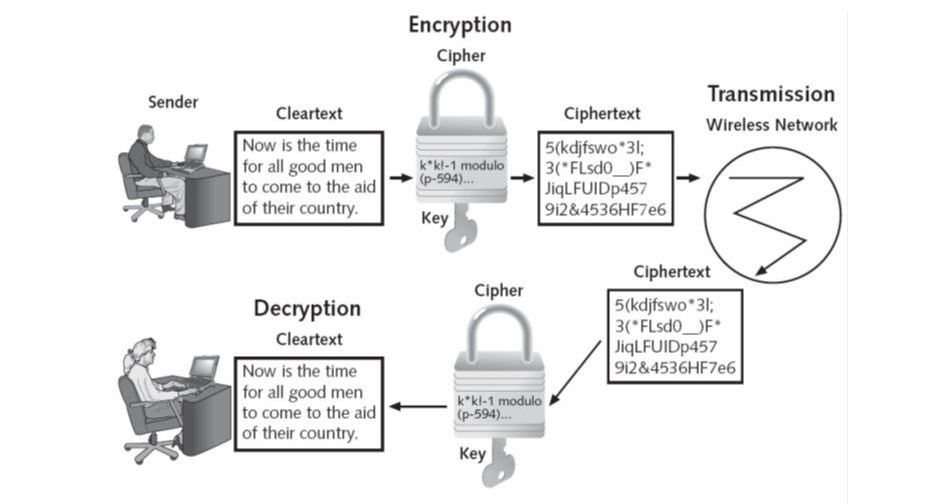
Wired Equivalent Privacy (WEP) Security || WEP encryption and decryption || WEP Insecurities
Wired Equivalent Privacy (WEP)
The Best Wi-Fi Security Protocol: WEP, WPA, or WPA2? | AVG
WeP MPS - Apps on Google Play
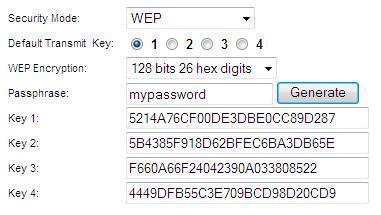
WEP Key Passphrase - Tech-FAQ

WEP vs. WPA
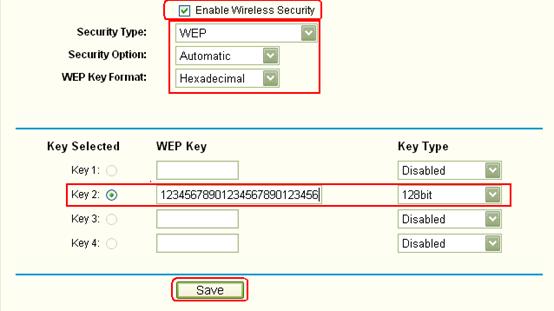
How do I secure my wireless network by using WEP encryption on TP
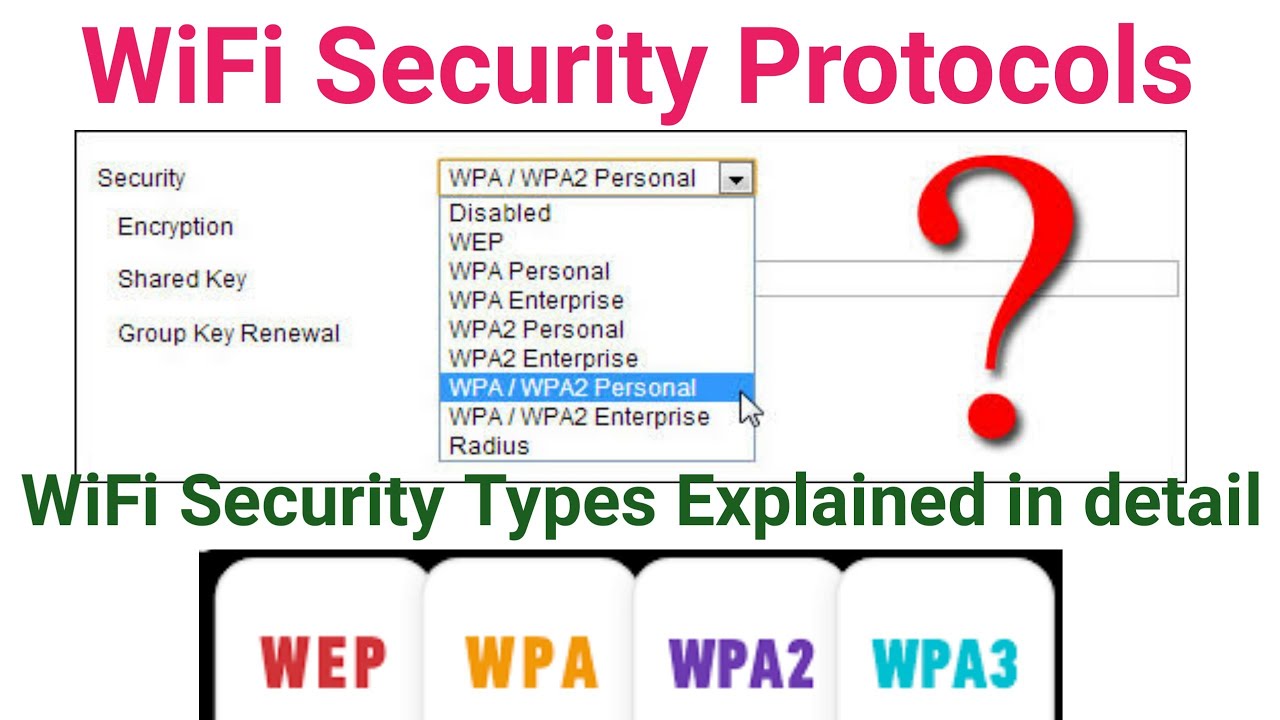
WiFi Security Types : WEP, WPA, WPA 2 & WPA 3 | WiFi Security Types explained in detail
, a security protocol for wireless local area networks (WLANs) defined in the b standard..jpg)
Wired Equivalent Privacy (WEP) - ppt video online download
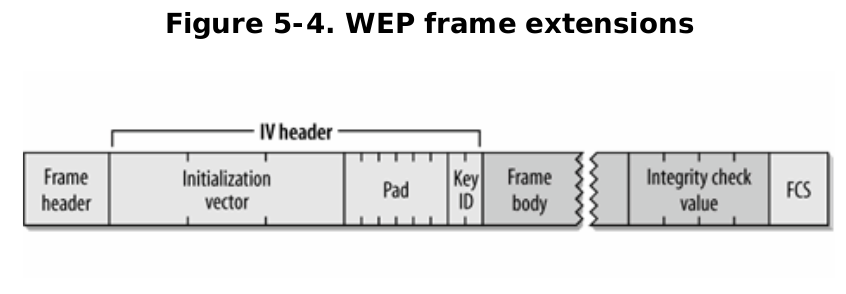
WEP Encryption and Its Vulnerability in Detail

WPA Key, WPA2, WPA3, and WEP Key: Wi-Fi Security Explained

What is Wi-Fi Protected Access WPA - zenarmor.com
WEP Clinical

WiFi (Wireless) Password Security - WEP, WPA, WPA2, WPA3, WPS
WEP
WEP Vs. WPA or WPA2

The Difference Between WEP, WPA, and WPA2 Wi-Fi Passwords ?




商品の情報
メルカリ安心への取り組み
お金は事務局に支払われ、評価後に振り込まれます
出品者
スピード発送
この出品者は平均24時間以内に発送しています














